
 |
|
| HOME | CURRENT ISSUE | |
Stronger customer security and FFIEC compliance are high on enterprise 'To Do' lists. Here's what to look for in a solution.
Online fraud has become big business, threatening customer
confidence in e-commerce in general and banking transactions in
particular. While that should be sufficient motivation to strengthen
fraud detection and prevention programs, new federal guidelines have
given security managers leverage to implement the technologies and
processes they need to protect their business.
This couldn't come at a better time, given the in-creasing sophistication of phishing and other attacks.
"The bad guys online are getting more sophisticated in their attacks," says Lee Carter, president of online banking for Zion Bank, based in Salt Lake City. "It used to be easier to pick these out because the phony emails were poorly done, with typos and grammatical mistakes. But now, the emails are better crafted and more believable, and they mimic the tone and tenor of the targeted institution."
Dozens of vendors have stepped up to provide various technologies, including some innovative ones that make use of real-time verification calls to purchasers' cell phones and other methods that make it harder for keylogging programs to capture user names, passwords and bank account numbers.
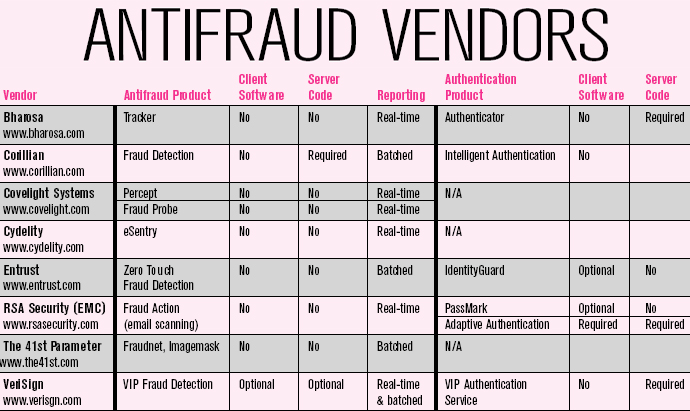
The three biggest vendors in this area are VeriSign, RSA Security (recently acquired by EMC) and Entrust. Each has multiple product lines that are being used to satisfy the Federal Financial Institutions Examination Council (FFIEC) guidelines and can be used by non-financial firms, as well. In addition to the big three, a number of smaller vendors have specialized products in one or both areas.
So how do you pick the right player? It isn't easy. The various vendor Web sites are long on architectural vision and short on specific product information, let alone pricing details. We interviewed a number of vendors and spoke to several typical customers to come up with some practical guidelines to help you choose the solution that best fits your organization's strategic needs.
No Simple Answer
FFIEC
guidelines recommend that financial institutions adopt stronger
authentication and fraud detection methods for fund transfers, and
situations where a customer's identity and other account information is
accessed. (See "What's FFIEC?".)
Immediate detection and prevention are essential, since financial
transactions happen in real time; banks don't have the luxury of
stopping shipment on that high-def TV after the fraud is discovered.
"The good news is that physical goods don't ship in real time, so e-commerce sites could make more use of out-of-band detection systems that don't require as much call center support as banks and others that have to make fraud decisions during the course of the transactions," says Bob Ciccone, CEO of Cydelity, an antifraud vendor.
The bad news is that the stronger authentication isn't likely to show up in consumers' hands anytime soon.
"The problem with third-factor, biometric authentication technologies such as retina scans or fingerprint readers is that people expect them to work as flawlessly as they do on the TV show '24,' and, at this point, they're not quite there," says Nick Selby, senior analyst and head of the security practice at The 451 Group, an industry analyst firm. Nor are secure hardware tokens going to be widely deployed to the mass market.
"E*Trade is using RSA's SecurID for its high net-worth traders, but it is interesting to note that this was a deployment driven by marketing, not necessarily security budgets," says Selby. "People feel safer when a fob protects their accounts, but widespread consumer deployment of hard tokens would be impractical and expensive."
The FFIEC guidelines were created to increase security for the online banking world, making it more difficult for phishers and identity thieves. But the same technologies that have been chosen over the past few months by most of the largest banks and brokerage houses make sense for any company serious about protecting online commerce.
Picking Your Solution
We
examined vendors that are on the leading edge in terms of integrating
with online systems being used by the largest banks, or who have
partnered or complement solutions offered by the big three and offer
some form of fraud-detection mechanism.
We didn't cover the numerous third-party e-commerce providers that handle storefront checkout and payment processing. With some of these players, such as 2Checkout.com and CheckFree, or online payment processing services from Braintree, merchants can accept online payments securely and customers are assured too.
Our discussions revealed several key issues that any company implementing these products should examine carefully.
Client software. Some products require a software client, cookie or flash object be installed on the user's machine, while others work without having any residue on the client PC--called "zero touch." This is not a trivial issue; institutions can't always depend on any client pieces either because customers may block software or because they change PCs that they use to access online services.
Some vendors give corporate customers the choice, as some institutions have explicit policies about client software on customer computers.
There are advantages and disadvantages to both methods. Clientless solutions have a harder time identifying fraudulent PCs. Placing a cookie or running some browser-based (e.g., ActiveX or JavaScript) object that stores information makes it easier to recognize when a customer uses that PC and returns to the e-commerce site for another transaction, and for the site owner to correlate any fraudulent uses of that PC. However, some customers prevent cookies or ActiveX controls from saving information to their PCs.
Most of the smaller vendors are designed to operate with no client residue, while the products from the big three vendors can support either mode.
"We have the option of being completely clientless to maintain convenience for the consumer and reduce their support burden," says Kerry Loftus, a director of product management for VeriSign, "but we've found that some banks are willing to look at solutions with some kind of PC."
All of the fraud-monitoring products look for common usage patterns and characteristics of each transaction (see "The Four C's"), such as a time of day and day of the week a customer is using a particular Web browser from a particular IP address on this ISP from a particular location. This takes into account customers who use multiple PCs at home or at work, but log in to their e-commerce site in predictable patterns. The fraud screeners can aggregate this behavior and look for anomalies, such as a login from another country or when a user has switched to a different browser version.
Impact on the infrastructure. Depending on your environment, you will need to consider whether any changes have to be made to existing production data streams and commerce servers to support these systems. Just as there are some products that don't have any client residue, there are some products that work inline and without any modification to production networks and existing e-commerce system code. Organizations looking for quicker deployments are obviously more interested in products that don't touch their production servers.
Covelight Systems, Entrust and Cydelity, for example, sell appliances that are installed on a customer's DMZ and essentially capture traffic that comes across the network.
"We just need access to a span port or a physical network tap on the client network. There is no code to write, nothing to change with the applications," says Covelight CTO Garth Somerville.
Others, such as Corillian and RSA's Adaptive Authenti-cation, require JavaScript or .NET code to be inserted in the online application to connect to the fraud or authentication system.
Granularity of detection. The choice here is between good detection and good enough detection. Can the software determine individual fraudulent transactions, or is it limited to blocking potentially fraudulent logins from spoofed PCs or keyloggers? And does it cover other malicious behavior, such as site copying for phishing attacks?
Phishing attackers, for example, go through a predictable pattern prior to actually getting victims to cooperate and send account information. First, they make a copy of the main pages of the target e-commerce site and store these pages on a phony Web server. Next, they harvest a bulk list of email names and send out a mass mailing. Finally, the victims will click on these links in the emails that take them to the phony site.
Corillian, for example, can detect this kind of activity by examining email for phishing come-ons. It accomplishes this without placing any hardware inside a customer's network, while other vendors need to be on the inside of the corporate network to capture this kind of information. Corillian puts its collector agents at major Internet peering points and is scanning the email traffic for mass mailings. It can then alert customers that a potential phishing attack is brewing and shut down access to the phony site.
"We can catch phishing sites while they are still being set up because we track behavior such as copying the site home page and other details," says Greg Hughes, CSO of Corillian.
Authentication options. Some applications are mere passive observers just sending alerts to a central monitoring console when a situation is detected. The big three, as a result of aggressive acquisitions, have lots of choices here. "We can deliver a whole range of authentication methods on a single software platform, says Entrust CTO Chris Boyce. Entrust has purchased Business Signatures over the past year, while RSA bought PassMark Security and Cyota.
Some technologies, such as those from PassMark, actually intervene at login, presenting a user with escalating multifactor procedures such as challenge questions that he has specified beforehand. Others, such as Corillian's Intelligent Authentication and VeriSign's VIP Fraud Detec-tion, can actually dial the user's home or mobile phone number and request that a PIN be entered before proceeding. Identity theft and fraud detection vendor Bharosa puts up a JavaScript image map of a keyboard to deter keyloggers.
The more invasive the authentication method, the higher the call center support volume if not implemented properly. Many of the vendors we spoke to cited Bank of America's large-scale deployment of RSA/PassMark's SiteKey in 2005. Call center activity increased, and many customers resisted using this technology, which asks them to match a particular image and stores a cookie on the user's machine to identify subsequent logins.
"Our biggest impact after implementing Corillian's Intelligent Authentication system was the increased call volume into our contact center," says Eric Bangerter, director of Internet services at the University of Wisconsin Credit Union. "Some of our members had questions with how the system worked, and a few were unhappy with it and didn't appreciate the added security."
Corillian's product tracks the PC profile (IP address, ISP, country of origin) to determine if a customer is using established patterns and machines to access their bank accounts. The credit union brought the support issues under control by improving online help and tuning how it implemented the strong authentication.
"The average consumer isn't willing to invest much energy in doing stronger authentication," says Amir Orad, VP of marketing for RSA's Security Consumer Solutions Division.
Timely reports. Some products make reports available in real time, while others are more appropriate for overnight batch jobs. This depends on the particular product involved and what kinds of reports are required, along with how the system will send out its notification messages and whether the vendor maintains its own 24x7 service-monitoring center for its customers. Covelight, Bharosa and RSA's Fraud Action are all best used for real-time analysis.
"If you don't buy into the server integration approach, you have to look at the log files for anomalous or fraudulent behavior," says VeriSign's Loftus. "So how near-real time your reports are really depends on how often those logs are rolled over. If you want more real-time reporting, you need to integrate something into the server applications."
Reconnaissance intelligence. Another issue is the ability to share fraudulent IP addresses and other information across a vendor's entire customer base, similar to how antivirus security response teams work to track infections. This opens many different possibilities for institutions to choose the appropriate solution, from the big three to electronic payment processors.
RSA leverages this omniscient view in its Fraud Action product, and VeriSign has something similar across its product lines.
"Sixty percent of all fraud attempts are being caught by just looking at this network because we have such large customers," says RSA's Orad. As another approach, CheckFree's FraudNet has teamed up with analytics partner Actimize to provide real-time fraud analysis across its electronic payments network.
Integration challenge. Finally, does the vendor offer stronger authentication, ID management and fraud detection products that work together, or can you mix and match both pieces from different vendors?
The big three are busy integrating their diverse product lines, such as having their fraud screening tools provide feedback on questionable situations so that their stronger authentication systems can provide additional challenge questions at login. Given their rapid acquisitions pace, they still have some work to do.
The smaller vendors are also working hard to connect their fraud detection systems with stronger authentication products, but working with the big three competition's products doesn't seem to be a priority.