
 |
|
| HOME | CURRENT ISSUE | |
Enterprises have a pressing need for endpoint security, but choosing a system that screens PCs before allowing them network access requires careful consideration.
Without a doubt, endpoint security is one of the top challenges
facing the enterprise today. In fact, readers rate strengthening
endpoint security as this year's top identity and access
management-related challenge in Information Security's 2007 Priorities Survey.
The rise of the mobile workforce has put the spotlight on endpoint protection. More than ever before, employees are plugging laptops into networks remotely, putting companies at risk for viruses, worms and spyware. Consultants and suppliers running unmanaged PCs compound the risk.
There are dozens of products that claim to solve this problem by making sure laptops and other endpoints are virus-free and otherwise secure before allowing them onto the network. These appliances work with standards being developed by Microsoft, Cisco Systems, Juniper Networks and others to assess PC health and provide some form of remediation and network protection.
But before you open those ornate gates to your network and install just any old virtual callbox, there are four questions you need to ask about endpoint security. The answers will help you choose the product best suited for your organization.
What security infrastructure do you have in place?
The
first step is to understand your existing security portfolio and where
the endpoint solution will fit. Depending on what you already have in
place, you may duplicate what the various endpoint solutions provide.
Some products come with intrusion detection and prevention systems or VPN gateways that are part and parcel to the endpoint security solution, while others work with existing IPS, IDS and VPN products. If you don't have a VPN and are looking in that direction, Juniper and F5 Networks (and, to a lesser extent, Cisco) provide VPNs with fairly solid endpoint health-scanning features. It is important to realize that your endpoint security will cover only machines that remote users are running and won't scan any local network users' machines.
It's also important to understand that just because one vendor supports another vendor's VPN or IPS doesn't mean that this support is seamless, or that you can create a single repository of security policies to cover remote and LAN connection scenarios. For example, AEP Networks offers an SSL VPN product as well as the separate NACpoint endpoint security product, but the two don't share a common security policy repository and won't be integrated until sometime later in 2007. In the meantime, the NACpoint line supports a wide array of other VPN products.
At the other end of the integration spectrum is Juniper's Unified Access Control. "Administrators can share their remote access and LAN access control policies between the Secure Access SSL VPN and endpoint security platforms, ensuring consistent access control policies between LAN and remote access scenarios," says Juniper spokesman Roger Fortier.
Examining other products more closely reveals additional nuances. For instance, Lockdown Networks' Network Access Control device doesn't have any IPS functionality, but works with Enterasys Networks' Dragon IDS appliances and recently added its own VPN features. While most of the products offer general support for IPsec VPNs, InfoExpress' CyberGatekeeper also supports SSL VPNs from Nortel Networks, F5, Juniper and Aventail. ForeScout Technologies' CounterACT offers specific support for Check Point Software Technologies' VPNs and will add support for Juniper and Nortel VPN lines soon. Vernier Networks offers two different EdgeWall models, the 7000 and the 8800; the 8800 includes its own IPS, and the 7000 model has its own IPsec VPN features.
There are other components that may be part of the endpoint package that could duplicate your existing network infrastructure, or at least have to learn how to play nicely with what you have. For example, Symantec's Network Access Control makes use of its own RADIUS server and additional software installed on Microsoft's Active Directory to handle DHCP assessments. And MetaInfo replaces your existing DHCP servers with its own to handle its version of endpoint security.
Another issue to consider is whether your endpoint solution will require network upgrades. For example, both Nevis Networks and ConSentry Networks offer their own 48-port switches with integrated endpoint security features, which could be expensive if you don't want to replace your existing switch infrastructure.
What are you really protecting?
Next,
you need to decide where on your network you intend to place the
appliance, and what part of your enterprise computing resources you
want to protect. Some appliances should be placed directly behind the
corporate firewall, covering the entire network; others are better
positioned behind the distribution switch layer, in front of critical
servers, or deployed to protect particular subnets or departmental
networks.
Some devices operate inline, meaning that any network resources located behind them will be protected, and only healthy network clients can pass through and gain access to these resources. Others operate out-of-band and are typically connected via a span port, watching over all of the network traffic on that particular subnet, and insert themselves into the network stream once a user has successfully authenticated through an Active Directory or VPN login. StillSecure offers both methods.
Part of understanding where to place these devices is in understanding the relative throughput that each will be able to handle passing through it. Juniper's endpoint solution covers a wide range in throughput, from 75 Mbps to 30 GBps. Some of the other products are limited and can't handle the higher throughputs of larger networks.
What is your deployment strategy to desktops?
Each
product uses a combination of software agents to scan the endpoint and
make determinations about its health. This software also may act on the
health information for remediation of the endpoint and protecting
network resources.
There is a lot of work for these agents to do. They have to examine open ports and running services, look through the file system for any rogue files or malware, monitor Windows registry keys, keep up to date on antivirus signatures, and check whether a personal firewall is running or has been tampered with. With some products, all this scanning and checking can extend the login process by several minutes, which could flummox users who expect something quicker and might call tech support before the agents let them log in.
There are three basic types of agents that can potentially be used by each appliance:
The thick agent is the easiest to understand, but the hardest to universally deploy; it means that IT must be able to manage and control these systems. In most cases, the thick agent requires that each desktop allow administrator access for Windows because you are installing software on every machine. Most of the vendors offer a thick agent for Windows 2000/XP, and some--such as AEP, InfoExpress and Lockdown--support Mac OS, too. A few vendors, such as Symantec and ConSentry, announced Mac support late last year or anticipate it will be added to their product lines in the next few months.
The thick agent is usually able to do the widest assessment of endpoint health, including scans of the Windows registry, file system, system services and open ports to determine if the machine has been compromised. It is also able to perform the remediation tasks to bring the endpoint back into compliance.
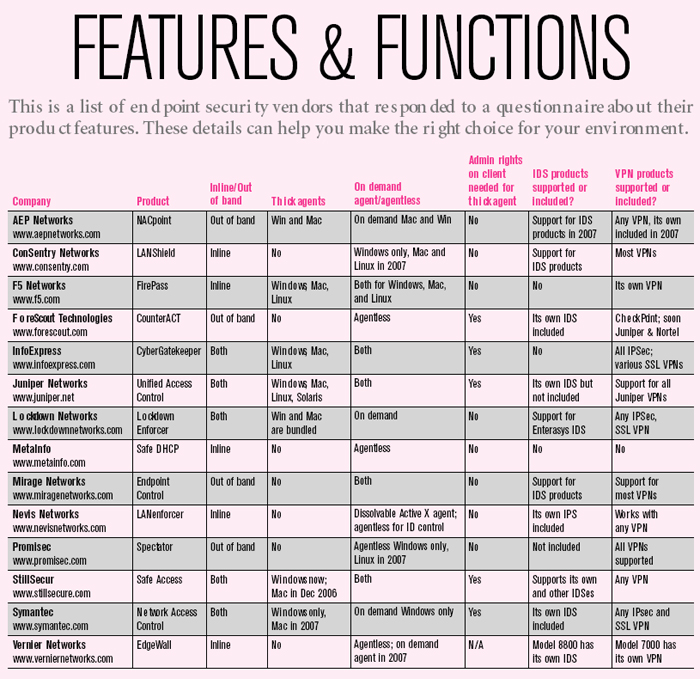
The trouble comes with unmanaged PCs that fall outside the control of IT, such as those being used by guest workers or business partners. This is the hairy edge of endpoint security, and the one that you'll need to scrutinize carefully to understand the differences among the various vendors. (See "Features & Functions".)
The issue is that an infected machine may damage your network prior to any login just by jumping on a particular network segment. Most of the vendors have this situation covered by doing some kind of rudimentary health assessment prior to providing an IP address or other network credentials to an endpoint.
On-demand agents can cover the unmanaged PC because the agent doesn't get delivered to the endpoint until the machine tries to connect to your network. These typically take the form of a JavaScript or Active X control (or both) that are loaded via a Web browsing session at the time of connection, similar to how SSL VPNs work with browser-based clients.
Some of the on-demand agents actually clean up after themselves, what the industry is calling "dissolvable" agents. "An auto-uninstall option allows our agent to self-dissolve at a specified time, which is ideal for ensuring compliance on guest devices," says Dan Clark, a marketing manager at Lockdown.
Lockdown and Mirage Networks take things a step further: Both companies place each endpoint on its own private VLAN, thereby ensuring that risky devices remain isolated from others. "We surgically isolate devices and do not integrate with switches to place all infected devices into the same VLAN because this facilitates cross-contamination," says Grant Hartline, CTO of Mirage.
These on-demand agents are specific to particular operating systems and browser versions, and while most support Firefox and Internet Explorer, there are fewer options as you move away from Windows OSes. ConSentry has on-demand Windows agents and plans to offer Mac and Linux ones later this year, but other vendors have been slow to support non-Windows systems.
Finally, there are the agentless approaches, which sound peculiar but are actually quite clever because they leverage something already present on the endpoint that the security system can query. Typically, these don't offer much in the way of remediation, but they do offer some minimal authentication verification. Again, these are OS-specific pieces of software.
Do you have to manage non-PC endpoints?
Part
of figuring out the agent landscape is in knowing what else is on your
network and what you need to manage. Thick agents can't manage non-PC
devices, such as print servers, network cameras and PDAs that are on
the corporate network, run their own operating systems and have IP
addresses. They can't be easily controlled by an endpoint appliance.
Nearly all of the vendors offer the ability to white-list or
pre-authenticate their MAC or IP address, so the devices can still
connect to the network and do their jobs.
But what happens if these embedded devices become infected? ForeScout's CounterACT has this covered. It provides the ability to detect these devices and apply policies that would safeguard the network from security threats emanating from them, says Gord Boyce, ForeScout vice president of worldwide marketing.
"For example, a policy can be established to ensure that traffic coming from a network printer is specific to print-related traffic," he says. "If the printer begins to act like a different device, as in the case of someone spoofing the printer's IP address, the CounterACT system will detect the change in traffic and quarantine and/or disconnect the device."
Others, such as Mirage, also monitor these devices to make sure they don't turn into threats down the road.
Clearly, figuring out the various bits of a complete endpoint security solution isn't easy, especially for heterogeneous enterprise networks with a wide range of devices and operating systems. While today's appliances help companies deal with a pressing problem, there is hope that as Microsoft, Cisco and the Trusted Computing Group continue to develop their standards and offerings, the job of endpoint security will become a little easier tomorrow.